Open Source is emerging in the enterprize as the true leader. True leader because it truly addresses the needs of the user community. Its happening all around us. Not because I am keeping an eye to it but just that its getting embedded in all our activities, appliances and daily life. Look at the OLPC, it will have Wikipedia all setup to provide kids to get on to the "real and correct" source of information when looking for it. Keeping same things close to our heart we will do some investigation and play with this router.
I have the Virtual Appliance ready and have sent an e-mail to the Vyatta guys to see if they have any objections on it. I will test it on a VMware player, WKS and VMware Server. I will make it available here and also pass the link to the VMware Appliance directory.
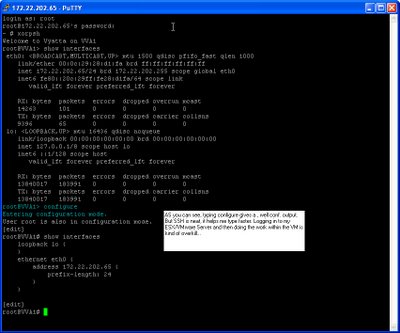
In the meanwhile check out some screenshots...(It's all grub but you won't mind typing, would you)
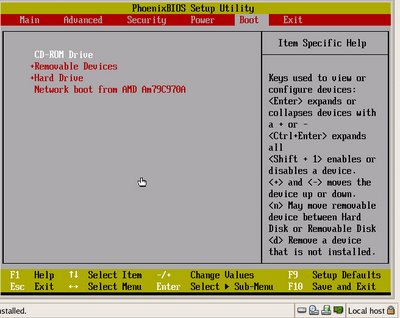
Change boot options (press Shift and +/- to change order)
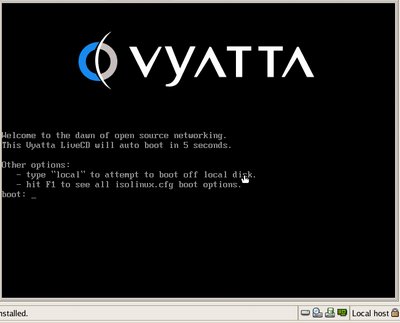
Vyatta loads, user/password = root/vyatta (This will remain same for the virtual appliance as well)
Type ? for command line options
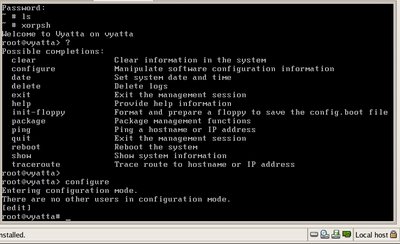
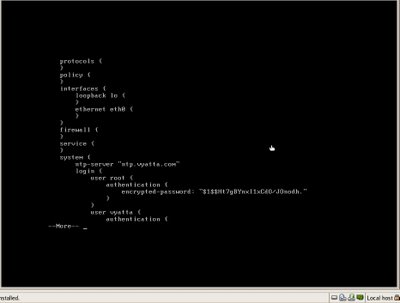
For instance typing "show" gives you a long list of conf. If syntax gives you headache type q to break
Show version command gives you the version of the image...

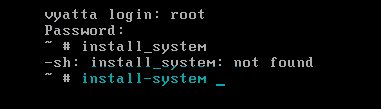
Installing is pretty easy too...type "install-system" (Don't do it in XORPSH
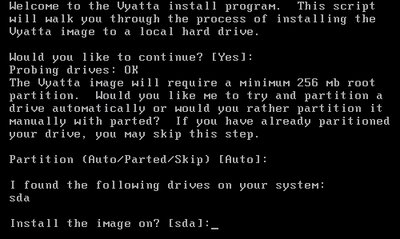
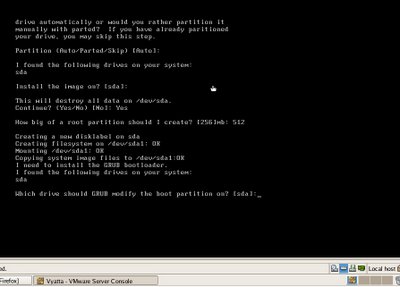
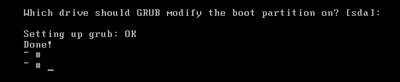
Choosing "Yes" to all options will get you to have an up and running router!
Lets now check a quick basic configuration:
(OK before I put this up, I will pick this VMware created appliance and import it into my Workstation environment here at my home domain). Its a small 55mb appliance so it won't take too much time.
I was able to load the appliance on my VMware workstation. I just did not have a floppy drive (who has them these days anyways), I may just create a virtual *.flp drive for it if it needs it that bad.
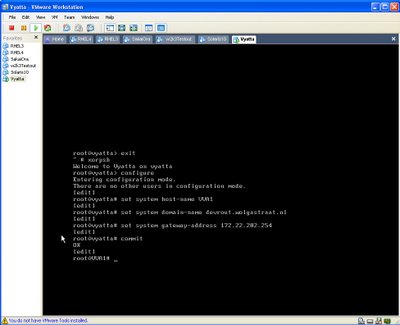
Basic Configuration: Setting up Hostname, IP address and Default gateway
====================================================
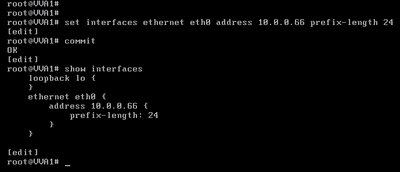
Configuring Ethernet:
===============
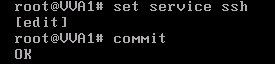
Setting up services:
==============
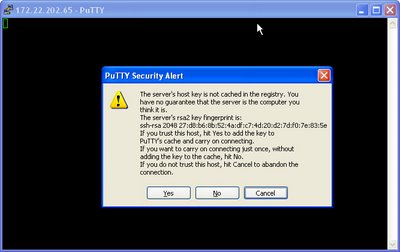
And eventually doing it from SSH by setting up PuTTY

Say YES,
We'll be going through more of the advance configurations and other aspects such as
to name a few.
Comments
Post a Comment