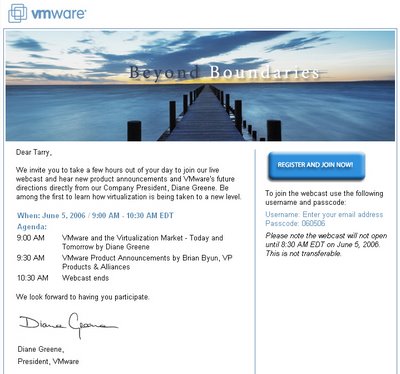
A personal letter from Diane Greene! :-).
Diane is my hero for a lot of reasons (The fact that I talk about her vision on the company and the core geek group that she leads and how she leads!!! It already says enough of why we tend to talk virtualization and VMware in the same tone).
I had already applied to it but is always pleasing (if not flattering enough) to be asked personally to attend. (I know, I know. It's an automated electronic mail all set to be fired to all known fellas but I'd like to hold on to the idea that it was sent to me. It is that personalized message and word of mouth that has brought VMware to where it is today).
And where it is set to go is something most competitors can not possibly imagine. And talking about the future of virtualization (I've spoken about it at several occasions both on my podcasts here, here and here and on my blog on several occasions like this one
But like I said we aren't all mouth but all ears as well...
Comments
Post a Comment