Last night I've been busy setting up the Samba4 on my VMware Workstation. Installation went fine. I'll add the print screens and the rest later. We will also try to start playing with ADS and trying to pump all data, migrate users and the rest , bring the Windows PDC down and activate our Linux directory.
More coming soon...(as in tonight ;-))
Where do I get it?
OK A quick look at the installation. Remember a couple of things. This is a TP (Technology Preview), so don't go rushing into your environment and upgrading your Samba3 yet. Wait. Hey that's why we have VMware machines. No harm at all. We'll even make a copy of a sample ADS in VMware and do some fun stuff.
But OK first setting it up.
- Unzip it (tar xzvf ...)
- Go to the source directory.
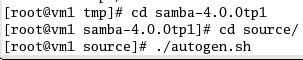
- Run ./autogen (see below). Since this is no release yet, you have to generate scripts by hand.
- and then ./configure
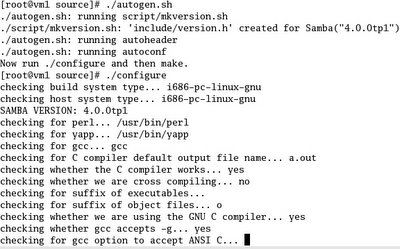
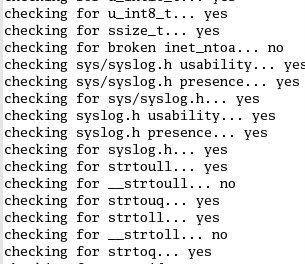
- Checking...
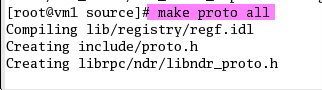
- make proto all (if your GCC version is above 3.4 you can do it a lot faster (five times faster they say) then do make pch all
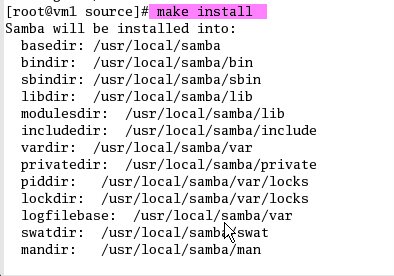
- Time to install
- And then Provision...
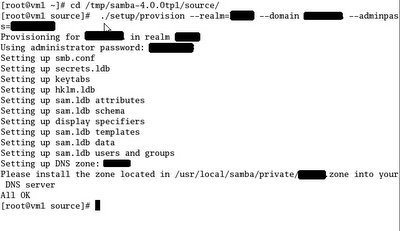
- Creating a simple smb.conf
The provisioning will do that with no shares so you need to make one here yourself.
[myshare]
path = /tmp/test
read only = no
- Starting Samba4
The easiest to just run "smbd", but a curious soul will do this inadvertently
# smbd -i -M single
This will "start" smbd without messages in stdout, and running a
single process. That mode of operation makes debugging smbd with gdb
easy.
Also note that you don't need to have an Samba3 nmdb instance running. So if you are running any , stop them before you start Samba4.
Make sure you put the bin and sbin directories from your new install
in your $PATH. Actually you should do that already before provisioning!
Next we'll continue testing and playing around ADS and even go to lengths of pumping the life(data) out of Windows PDC and shutting it down and replacing it with Linux based PDC.
Comments
Post a Comment