Ok this is real cool, all you need is to copy and paste this code(courtesy consumingexperience.blogspot.com, the guy who started Technorati) . So what I did was.
o Install my language packs(for east asian languages).
o Restarted my computer(gee..that you so have to do, if you're on a microsoft machine)
o The code, in JavaScript and HTML
o I pasted this code just under my post tag, you can also put it all above
Ok so we're back, cool movie Madagascar, by the way.
PS: For Japanese, Korean and Chinese you'll need to install language packs on your XP machine, or else you'll see lot's of pipe bars.
If you're not seeing this on for the Japanese, Korean or Chinese then you need to install the language packs(On *nix machines it should be installed). If you have XP/2000 then you might want to install the language packs. See below.
Click on it and then Install them, you will be asked for the installation CD.

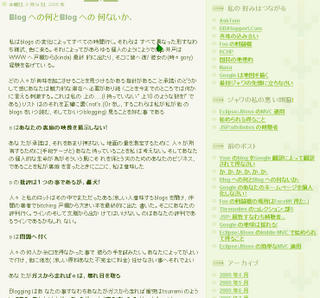
And then clicking on, for instance a japanese translation you'll see this page.

and upon clicking for translation you get this...
or if you'd rather want it in spanish.

If you want it(the translation) to open in the same window get rid of all the _target=blank in the Template code.
Ok so as you see I went ahead and replaced the JavaScript with the HTML code. The code was placed between [blogger] and [/blogger]
and here it is
<a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cde&hl=de&ie=UTF-8&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">Deutsche</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Ces&hl=es&ie=UTF-8&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">Español</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cfr&hl=fr&ie=UTF-8&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">Français</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cit&hl=it&ie=UTF-8&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">Italiano</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cpt&hl=pt&ie=UTF-8&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">Português</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cja&hl=ja&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools"> ���</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Cko&hl=ko&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools"> í��êµì�´</a> | <a href="http://translate.google.com/translate?u=<$BlogItemPermalinkURL$
>&langpair=en%7Czh-CN&hl=zh&ie=UTF-8&oe=UTF-8&prev=%2Flanguage_tools">æ±�è¯</a>
All I did was
o Replace the $BlogURL$ with $BlogItemPermalinkURL$

and then replace it all...

o removed _target="blank"
Try it out!
Tarry
Comments
Post a Comment