Companies are talking about virtualization all over the place and all the time. There are vendors and resellers who have (sometimes) no clue at all as to what it is and what should we implement? What should we actually advice a client? What and where would they want to achieve virtualization? On the Server level? I did post some stuff on Virtualization on the Server Level with VMWare. But it all comes down to applications!
How on earth are you going to implement a Windows to Linux Migration for all desktop applications? And then comes the interesting part, if I do propose a *Thin Client* solution where do I start if that part of applications suite (If you were doing this for say a University then you have a whole bunch of applications you will NOT just be able to run on Linux desktop) anyways you still have to move over from the Microsoft Terminal Server to something else. But what? VNC? RDP? Are they fast enough? Can the end user run his OpenOffice which we migrated (with his data) from his desktop as a thin client? And can he get just just about the same experience? Even via a dialup modem?
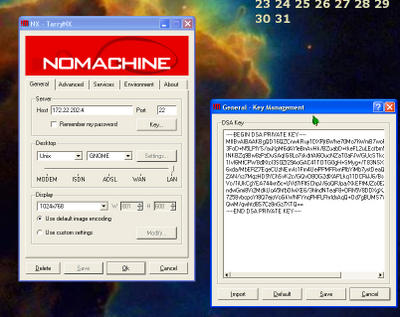
Then say hello to NXMachine or NoMachine (for paid services) or try the FreeNX. This stuff is supposed to run real fast, so I hear. OK without much ado, I took the words of the FreeNX guy for granted.
NX is an exciting new technology for remote display. It provides near local speed application responsiveness over high latency, low bandwidth links.
Ok so let's try to install it on our WBEL 3(at my work testing from home @800KB/sec) and RHEL 3(at my home , testing via a regular WLAN 54mbs/sec) systems and then try some Remote work using the !M stuff.
Scenario 1 : Testing via home, using RDP/MSTSC service to connect to a machine and then launching VNCViewer on Windows Server 2000 at work to log on to Linux Server. See print screen here...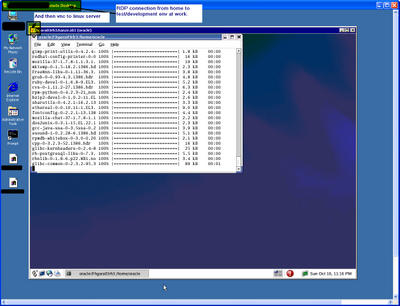
Scenario 2 : Testing the regular RHEL 3 VMWare machine on a PC at home WLAN(54Mbps/s) network. This is the situation here...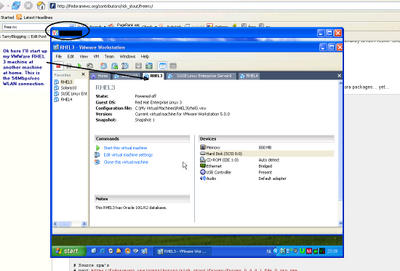
You will need to have that sshd/port 22 running. (OK from Windows people point of view, if you're able to PuTTY to that machine, you're cool :-))
Ok as we move on we'll need to...
- "yum update" or "up2date" logged in as root on our linux machine/server
- find if we have expect and nc, or else install them "yum install expect nc"
- Install the NX binaries on the client machine, go here to download them.
- Check out all the print screens on my foto.oraflame.com gallery and this article for a serious study on NX and it's competitors
Like I said ,check out the print dumps on my site for detailed step by step instructions.
Comments
Post a Comment