Saw this advert on Slashdot and went on to look for it and found the tour pretty neat to look at. Check out the demo too!
So why would I need it?
WHY NOT? I'd say. As an organization grows , new services, new data comes by, new logs start accumulating on the servers and it becomes increasingly difficult to look at all those logs, leave alone that you'd have time to read them and who cares about analysis as the time to look for those log files already makes your day, isn't it?
Well a solution like this is a cool option to have your sysadmins/operators look at ONE PLACE and thus you don't have your administrators lurking around in your physical servers and *accidentally* messing up things there.
Go ahead and give it a shot by downloading it and testing it. I'll give it a shot myself!
Ok so I went ahead and installed it.
Do this...
[root@tarrydev Software]# ./splunk-Server-1.0.1-linux-installer.bin
to install and this (if you screw up)
[root@tarrydev Software]# /opt/splunk/uninstall
to deinstall.
Installation is pretty neat GUI and you can't go wrong there (make sure that the ports are available)
And last but not least, start the server
[root@tarrydev Software]# /opt/splunk/bin/splunk start
Version is Splunk Server
Starting splunkd [ OK ]
Starting splunkSearch [ OK ]
and check it it's running
ps aux | grep splunk | grep -v grep
root 2178 0.5 2.9 837880 30532 ? Sl 16:05 0:00 /opt/splunk/bin/splunkd
root 2181 2.8 1.4 18804 15096 pts/1 S 16:05 0:01 python /opt/splunk/lib/python2.4/site-packages/twisted/scripts/twistd.py --pidfile=/opt/splunk/var/run/splunk/splunkSearch.pid -noy /opt/splunk/lib/python2.4/site-packages/splunk/search/Search.tac
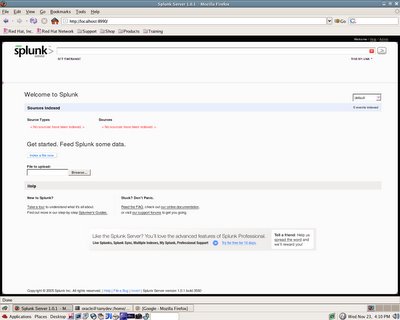
And here your Free Splunk Server with No data
and this one filled with IIS 5.0 data
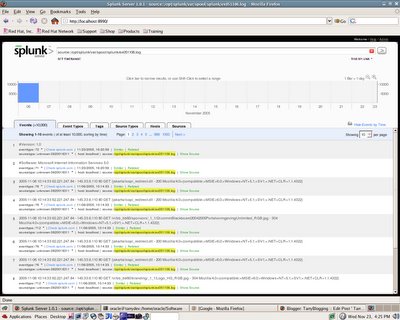
There's lot more to it than just Web Servers though and maybe Part II we'll check out some other servers.
Comments
Post a Comment